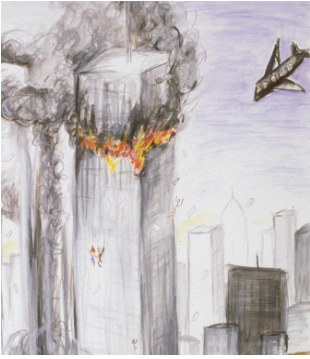
Terrorism is very scary, especially when it happens close to home and not in some faraway place. Nobody likes to be afraid, and we were eager to make the fear go away. So we demanded more security. In the last decade, it’s become increasingly normal for civil liberties to be eroded and for government agencies to spy on citizens, to collect and store their personal information. Regardless of whether you’re a fan of right- or left-wing policies, this affects every one of us.
So we have to take a look at the data and ask ourselves honestly, “Has all of this actually made us safer?”
The Beginning
After the attack of 9/11, the US government concluded that the law had not kept pace with technology. It created the Terrorist Surveillance Program initially to break communications linked to al-Qaeda. Officials were confident that if the program had been in place before 9/11, the hijackers could have been stopped. But soon the new powers were also used to prove guilt by association.
The FBI used immigration records to identify Arab and Muslim foreign nationals in the US. On this basis, 80,000 individuals were required to register, another 8,000 were called in for FBI interviews, and more than 5,000 locked up in preventive detention. Not one terrorist was found in this campaign.

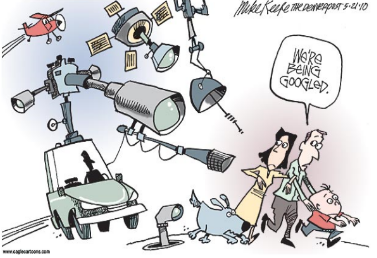
In 2013 Snowden leaked the document that reveals how the government sees and stores the private data of public. They showed how the NSA(National Security Agency) can demand information about users from companies like Microsoft or Google in addition to their daily collection of data from civilian internet traffic such as email content and contact lists. So, instead of focusing on criminals, governments are increasingly turning their attention to everyone. But if you are looking for a needle in a bundle of grass, adding more grass to the bundle isn’t going to make it any easier to find the needle.

On the contrary, every recent success announced by the NSA has come from classic target surveillance. Despite high hopes, the NSA surveillance program has not stopped any major terror attack.
Apple Vs FBI
In early 2016, the FBI asked Apple to produce a backdoor program to disable the encryption of a terrorist’s iPhone. Apple publicly declined, not only because this tool could be used to permanently weaken the privacy of law-abiding citizens worldwide, but fearing to open the floodgates for governments requesting access to a technology used by billions of people, a fear shared by security experts and cryptographers. A few weeks later, the FBI revealed that they had hacked the phone themselves, basically admitting that they lied to the public about the need for a backdoor, which questions how trustworthy spy agencies are in the debate about privacy and security, especially considering that the NSA, for example, already has the capability to turn on your iPhone microphone or activate your laptop camera without you noticing. Concerns about this are often met with the argument,
“If you have nothing to hide, you have nothing to fear.”
But this reasoning depends on person to person because if a person wants to keep privacy about own life then it doesn’t mean he/she is doing anything wrong. Right now, we live in a democracy. But imagine the damage the wrong person could do with our data because data is the new treasure of the current world.
The Government uses this law for own benefits
For example, following the November 2015 Paris attacks, France expanded its already extensive anti-terrorism laws by giving law enforcement greater powers to conduct house raids and place people under house arrest. Within weeks, evidence emerged that these powers were being used for unintended purposes, such as quashing climate change protests. The governments of Spain, Hungary, and Poland have introduced more restrictive laws on the freedom of assembly and speech.
If we talk about the FBI, then there is a case of former FBI director James Comey used this NSA data for his personal use.
There is also a case of Cambridge data analytica.
Indian Cases related to Data privacy :
Now if we talk about the case of India, this data privacy issue first come is light when aadhar card details were easily available. In Supreme court hearing Unique Identification Authority of India(UIDAI), the agency implementing aadhar repeatedly argued about Aadhaar that It will help against terrorism and banking fraud by ensuring that only “genuine” persons get access to mobiles, and banking services but in reality, the bank fraud cases were increased.
There is also a big question about how these aadhar card can be misused? Adhar card become more dangerous when other documents linked with aadhar. Imagine a third party hacker can access all your data like biometrics and bank account details then he can damage you in a bad way.
None of this is effectively helping us fight terrorism. The motivation behind this might be good, even noble, but if we let our elected governments limit our personal freedom, the terrorists are winning.
Then what is the Solution?
What’s worse, if we’re not careful, we might slowly move towards a surveillance state. The data is pretty clear: the erosion of rights, along with mass surveillance, hasn’t led to significant successes so far, but it has changed the nature of our society.
Terrorism is a complicated problem…
…without simple solutions.
No security apparatus can prevent a few guys from building a bomb in their basement. Creating master keys to enter millions of phones is not the same as searching for a single house. To take full advantage of this existing condition, we need better international cooperation and more effective security and foreign policies, better application of our present laws instead of new and stricter ones that undermine our freedom. We live in Democracy and we have our rights in our hands.
Keep reading, keep learning
TEAM CEV!
