author: aman
Blog V - Part II - Day 17
Hey People, I have given a gist of how the EVM stores the smart contracts on its machine.
In this I will directly discuss some technical things about, how deep you can dive into using just the information told about in the previoud micro-blog. Will try to give a glimpse, rest you can think of autonomously.
Let's do it...
In this micro-blog
- Ethereum Virtual Machine (EVM)
- The two Properties of EVM
- How the Smart Contracts are actually stored?
- Some supplementaries
- These trail of Digits have some meaning
- How can the attackers mis-use it?
Some supplementaries
I would suggest to open up following things in other tabs, would help you people throughout:
- Ethereum Virtual Machine OPCODES
- A Matrix of all kind of Gas Costs
- All Transaction Properties of Solidity
- EVMDIS Disassembler
These trail of Digits have some meaning
I will keep this explanation as vague as possible, as we have some people onboard who have excitement about the blockchain, despite their core interests and Fields.
You know right, EVM is a Stack based machine, as 2 + 2 is actually written as 2 2 +, postfix notation.
If you break this "strange series of digits", 608060405234801561001057600080fd5b5060016000819055506......
according to as shown in ethervm.io tab.
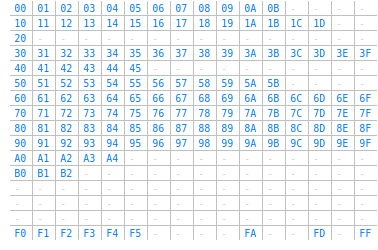
EVM is a stack-based machine and for actions to happend on this machine, these trails are converted into the OPCODES.
Each OPCODE has a size of 1 byte. EVM has a set of 140 OPCODES in total
| Byte Count | BYTCODE | OPCODE |
|---|---|---|
| 0000 | 60 | PUSH1 0x80 |
| 0002 | 60 | PUSH1 0x40 |
| 0004 | 52 | MSTORE |
| 0005 | 34 | CALLVALUE |
| 0006 | 80 | DUP1 |
| 0007 | 15 | ISZERO |
| 0008 | 61 | PUSH2 0x0010 |
| .... | ...... | .... |
| .... | ...... | .... |
| .... | ...... | .... |
Now, you understand how this thing works in EVM Stack? It would be infeasible to explain here how does a stack work. You better watch a video here call stacks & a big blog series here
If you are wondering how can you find the contract with that data? Well...just try copying pasting the following BYTECODE, and decompile in the ethervm.io/decompile, you'll find the same contract as was written in the previoud micro-blog simpleContract.sol.
608060405234801561001057600080fd5b50600160008190555060c6806100276000396000f3fe6080604052348015600f57600080fd5b506004361060325760003560e01c806360fe47b11460375780636d4ce63c146062575b600080fd5b606060048036036020811015604b57600080fd5b8101908080359060200190929190505050607e565b005b60686088565b6040518082815260200191505060405180910390f35b8060008190555050565b6000805490509056fea265627a7a723158200e135b4c7bcf7bde9dca1f257d97637d8137b315e29248b5654ac7830dab9e8264736f6c63430005100032
How can the attackers mis-use it?
The level of publicity, Blockchain provides, any user can directly use the address of the contract deployed, to instatiate a variable of that, contract and call its various function.
This is not small, this can let the potential attackers exploit the contract and cause big-attacks like, DAO-Reentrancy attack, or DDoS Gas attack, explained in the previous blogs.
As I have told, these work as the fill in the blanks, the vacant spaces within the Bytecode are initiated by 0 , which is then replaced by the hexadec code of the input.
This contract is again deployed to replace the existing one, changing the current state of the contract.
The Internal checks verifies whether you are the authorised one to make a certain check or not.
IG, This concept is heavily used in off-chains, as well.
====================
