Blockchain is often described as merely the technology behind the “Cryptocurrencies” and people fail to perceive the avenues it opens for the greater good of mankind. In reality, Blockchain is to cryptocurrency as to what the Internet is to email.
You never thought about applying blockchain in different domains for the upliftment of the society because you were too busy trading in Bitcoins and ether to mint money since that’s what you think the most about. (pun intended)
Do you know why blockchain is one of the hot research topics? Well, you don’t need to worry because we have got you covered. In this blog, we’ll go through the various prospects Blockchain offers to us, the challenges which can be tackled with the proper implementation and the hindrances which raise questions on its viability.
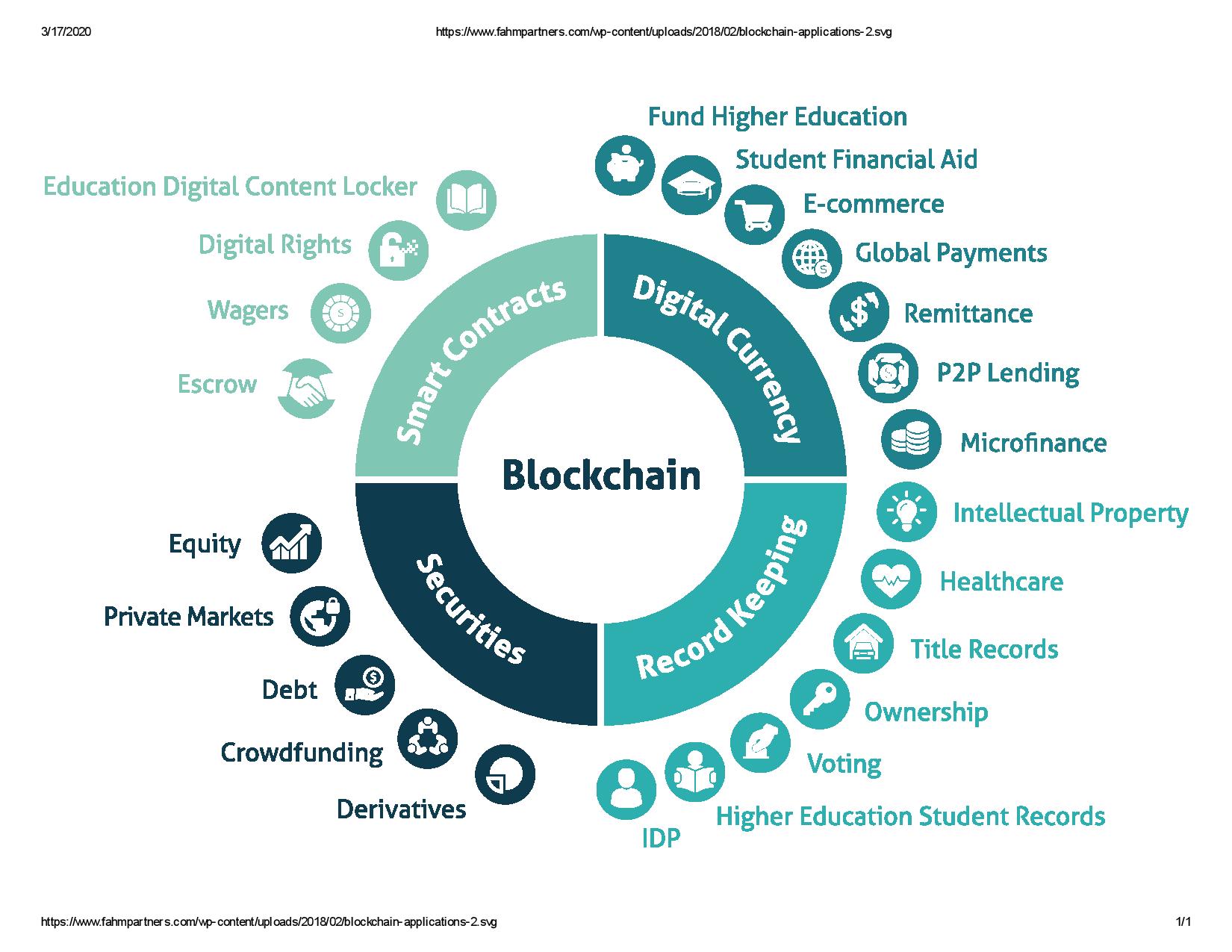
Applications of Blockchain
Confidentiality
- Aadhar and security of the citizens, from birth to death, all changes in our circumstances would be stored in a global decentralised system that cannot be altered without a trace that would log everything about that alteration. You get married? You insert the info. You need to provide proof for the taxman to get a deduction? You give him a code that would access only this information and nothing else. No more ID theft.
- One of the challenges hospitals face is the lack of a secure platform to store and share data, and they are often victims of hacking because of outdated infrastructure. Blockchain technology can allow hospitals to safely store data like medical records and share it with authorized professionals or patients. Moreover, this can improve data security and even help with accuracy and speed of diagnosis. For instance, your file would be online and your doctor will not have access to your cigarette addiction unless it will interfere with your liver treatment.
- Blockchain can come handy in Property rights. For instance, your step brother sells your garage but keeps the house of your grandmother? Recorded and accessible only for the potential buyer. The DNA analyser discovered your step brother has a stepbrother i.e. you then you will be added automatically to the property title even if you’re in Zambia and your phone will beep to give you the good news. (See how blockchain can make you rich even without Bitcoins)
Transparency
- Tired of not getting the RTI response on the latest government deal and expenditure? Blockchain allows you to check online what has been done on the 27.01.20 between 10.20 and 10.30 and see where is your tax money and what has been done (or not) with it.
- You give your 100 bitcoins for water infrastructure in Nigeria? You will see exactly where your money went and you won’t have the surprise of discovering that 99 went for the wages of the charity and one for the corrupted mayor that needed a pool in his garden.
- Blockchain potentially allows us the ability to vote in a manner that’s impervious to outside meddling or the influence of corruption. Creating an immutable, publicly-viewable ledger of recorded votes would be a massive step toward making elections fairer and more democratic.
- Even if your government is defaulting on its loans or your bank fails, you will still have an unaffected backup pool of money to draw from since many people were restricted to withdraw cash from PMC Bank and the most recent case being Yes Bank which can cause inconvenience to the ones who truly need it.
Payments and Transactions
- We don’t want foreign companies to track our day to day transactions like Gpay, PayPal or Paytm (Yeah Paytm is owned by Alibaba and Softbank) plus transaction costs are way lower.
- You don’t need to convert your rupees to dollars or yen every now and then. Blockchain can let you get rid of fiat money and lead to a much-stabilised exchange rate in future (no relation with “Future Markets”) unaffected by the happenings in the global trade and commodity markets.
- When you use credit and debit cards to make purchases (especially online), you’re trusting the vendor with information that other people could use to steal from you. This means that, if your financial information is stolen from the vendor, your money will be at risk.
Transforming the Economy
- Bitcoin’s value doesn’t fluctuate like market collapse like black Monday. In fact, Bitcoin emerged right after the 2008 crisis. Since cryptocurrency is still an emerging technology, the value of the various digital currencies can be volatile (discussed below), but the system was designed to not be inflationary in the long run. There are many aspects of cryptocurrency which contribute to its non-inflationary nature.
- Each cryptocurrency has a finite, set limit on the total number of coins that will come into existence. For example, the total number of bitcoins that can ever come into existence is 21,000,000
- There are controls and techniques in each cryptocurrency’s protocol that ensure that the process by which new coins come into existence is controlled and predictable over time. This means that we can accurately predict how much of a certain cryptocurrency will exist at any given time in the future.
- There is no money-issuing agency which can decide to mint more currency or enact fiscal policy that decreases the value of the currency. Just imagine the future where everyone will be trading in cryptos and not deal through dollars, yen and other troublesome conversions.
Eliminating Middlemen
- Eliminating the middleman (I call them leeches). You want to sell something, you access a free site powered by blockchain, list your item and sell it without having to pay ebay and PayPal commission. You want to sell a book? You can do it for 0.01$ and you could have 1m readers that would be willing to pay that 0.01$, not 1000 that would pay 10$ from which 9.9 go to the publisher and 1m that would download it from piratebay because they cannot afford to pay $10.
- You don’t need to purchase the expensive Netflix and Prime subscription to binge watch your favourite movies and series. Blockchain will give rise to the “Wikileaks of the common”.
- FACEBOOK owns three of the most popular social media platforms with in-app messaging service, Facebook, WhatsApp and Instagram respectively. Giving a private entity this much power is insanity at peak provided the recently infamous “Cambridge Analytica data crisis”.
Decentralisation
- Energy management has been a highly centralized industry for a long time. Energy producers and users cannot buy it directly from each other and have to go through the public grid or a trusted private intermediary. For example, “TransactiveGrid” is a startup using Ethereum that allows customers to buy and sell energy from each other in a peer-to-peer way.
- A completely decentralized internet, where ISPs aren’t needed anymore. This is what “Skycoin” does with Skywire. They will soon provide their custom built 1Gbps antennas for $100, which have a range of 10 miles and provide high speed internet to 7,000 people and with their mesh network on top probably 20,000 people. You only need 2,000 antennas per European country to cover the whole continent and the data is stored on Skyminers.
Information Security
- It’s interesting to note that multiple types of information theft keep occurring, way more than most people realize. A good example of this is the April 2014 “Heartbleed” bug in the openSSL cryptographic software. Hundreds of popular online services were hacked before the bug was disclosed, including big names like Facebook, Google, Instagram, Pinterest, Tumblr, Twitter, Yahoo, Yahoo Mail, Gmail, Dropbox, TurboTax, and GoDaddy.
- Ever got suspicious of the ad about the book in your Facebook and Instagram feed which you just added to your Flipkart wishlist? Companies like Flipkart, Amazon, Facebook, Google and many more are spying on your data making you vulnerable. Blockchain provides you the mask you need to stay safe from this virus (read corona).
- With the increasing role of IoT in our lives, it’s high time we stop trusting Siri and Alexa. Blockchain is one of the ways to protect our virtual presence and stop the ways MNCs manipulate us through the data they receive in various forms. Remember, data is the most precious thing out there.
Wastage of Energy
- The public Bitcoin and Ethereum blockchains use a consensus mechanism called ‘Proof of Work’ which requires all mining nodes to compete to solve a difficult cryptographic puzzle. However, the world-wide pool of computers performing this cryptographic puzzle creates significant electricity usage, most of which is ‘wasted’ by not leading directly to a successful puzzle solution.
- Though alternative consensus mechanisms are being developed for public blockchains, such as ‘Proof of Stake’, which do not use a computationally expensive puzzle, and will be markedly more energy-efficient, the massive redundancy in the large number of processing nodes in a blockchain system will always mean that more electricity is used than in a centralised non-replicated database. This is an inevitable trade-off for the distributed trust and increased availability offered by a blockchain.
Criminal Activity
- Through some third-party trading platform which supports cryptocurrencies, the user can either buy or sell any product. Since there is a high level of anonymity in this process, it would be very difficult to track the behaviour of the user, let alone the subject to legal sanctions.
- There are several methods fraudsters use to conceal their criminal activities, including altering or deleting information in a company’s accounting systems, changing electronic or paper documents and creating fraudulent files.
- However as pointed out by Ross Mauri of IBM Systems, “Using a shared digital ledger can help reduce fraud because it increases the visibility and transparency of the transactions made throughout a supply chain and between members of a business network. Participants can see the history and transfer of assets, so fraudulent transactions are easier to identify. Plus, to tamper with the transaction records on a blockchain, an individual or group of individuals in collusion would have to control a majority of the system.” So, the security claims remain disputable and prone to attacks.
Blockchain Efficiency
- The efficiency of blockchain themselves may become overloaded with complex consensus mechanism as well as invalid data. For example, most popular consensus mechanisms which are used in blockchain are proof of work, which is referred to as a “waste of computing resources” by the researcher.
- It is usually said that there are efforts to develop more efficient and hybrid consensus mechanisms that combine PoW and Proof of Stake (PoS). In addition to that, blockchain will produce a lot of information, data, transaction data, contract bytecode which may be useless and outdated.
- “There are several smart contracts which contain no code or totally the same code in Ethereum, and many smart contracts won’t be executed after its deployment. An efficient data cleanup and detention mechanism can be used to enhance the execution efficiency of the blockchain systems.”
Private Key Security
- Access to a blockchain requires both a public and a private key (the private key of the user is the identity and security credential). Keys are cryptic strings of characters of sufficient length to make the odds of guessing them truly astronomical. However, the user generates and maintains these rather than a third-party agency.
- An attacker can recover a user’s private key because it may not have enough randomness during the signature process. Once the user’s private key is lost, the user won’t be able to recover it again. Since blockchain does not depend on any centralized third-party trusted institutions, if the private key of the user is stolen, it would be very difficult to track the behaviours of the criminal to recover the modified blockchain information.
51% Vulnerability
- The level of vulnerability for attackers to control and exploit the entire blockchain in the consensus mechanism is 51%.To be specific, in the PoW-based blockchain, if a single miner’s hashing power accounts for more than 50% of the total hashing power of the entire blockchain, then it can result to the launching of the 51% attack.
- Hence, the concentration of mining power in some mining pools may result in the fear of an inadvertent situation, such as a single pool controlling more than half of all the computing power.”
Double Spending
- Though the consensus mechanism of the blockchain can validate a transaction, it’s still possible to avoid double spending or using the same cryptocurrency myriad times for transactions.
- The attacker can exploit the intermediate time between the two transactions initiated and confirmation so that an attack can be launched quickly.
Smart Contracts Vulnerability
- Smart contracts aren’t that smart after all. While being executed, smart contracts may have security vulnerabilities which are caused by program defects.
- A survey by ScienceDirect shows that 8,833 out of 19,366 Ethereum smart contracts are vulnerable to bugs like transaction-ordering dependence, timestamp dependence, and mishandled exceptions. Not to mention that smart contracts are also pretty under-optimized.
Untested Code
- Despite the nearly 8-year history of Bitcoin, blockchains not dedicated to cryptocurrencies are still heavily experimental. As such, some DLT creators are tempted to deploy insufficiently-tested code on live blockchains. One now-infamous example is that of The DAO attack. Aman already discussed this in his blog which you can access here.
- The hack resulted from the attacker exploiting two vulnerabilities in The DAO code. The hacker knew that the code was designed to allow both a split, and a transfer of tokens between accounts. The hacker also realized that the code would not update account balances fast enough to prevent transferring the same tokens more than once. Since the code did not decrement the original account balances after each transfer, there was nothing to stop the same tokens from being replicated about 40 times each, without the original tokens being destroyed and it was exploited to the extent that $55 Million worth of ether was transferred.
It was very exciting for me to come up with this and I hope you enjoyed it.
In future blogs, I would talk about the impact of blockchain in the economy and what it holds for us in the future.
Thank You for your time!
– Kaushik Chandra
Ist year : MSc – Physics