Khoor Hyhubrqh!!! L jrw qrwklqj wr vdb ;( wkdw’v zkb l dp hqfubswlqj wklv xvlqj d Fdhvdu Flskhu. L zloo frph edfn wr hasodlq Fdhvdu Flskhu lq ghwdlo lq wkh qhaw eorj.
~WHDP FHY
Definition and History:
Cryptography is a method of protecting information and communications through the use of codes so that only those for whom the information is intended can read and process it. The word ‘cryptography’ was coined by combining two Greek words, ‘Krypto’ meaning hidden and ‘graphene’ meaning writing.
The first known evidence of cryptography can be traced to the use of ‘hieroglyph’. Some 4000 years ago, the Egyptians used to communicate by messages written in This code was the secret known only to the scribes who used to transmit messages on behalf of the kings. One such hieroglyph is shown below.
Later, the people switched to simple mono-alphabetic substitution ciphers from 500 to 600 BC. This involved replacing the alphabets of the message with other alphabets with some secret rules or algorithms. This rule leads to a key to retrieve the message back from the secret message.
Why Cryptography?
The goal of modern cryptography is to ensure secrecy, integrity, etc. There are many attributes of information that can be assured in this way, but here are 4 big ones:
Confidentiality: It is to assure that only the intended recipient of a message can read it. This is what most people think of when they hear “cryptography,” and it is the primary goal of classical cryptography.
Integrity: It is to assure that a piece of information has not been altered. This is the purpose of message authentication codes (MACs), message digests, and cryptographic hashing.
Authenticity: It is to assure that the sender of a message is who they say they are. This is the realm of digital signature and public-key cryptography in general.
Non-repudiation: It means to ensure that the transferred message has been sent and received by the parties claiming to have sent and received the message. It is a way to guarantee that a sender of a message cannot later deny having sent the message and that the recipient cannot deny having received the message.
Basic Cryptography function :
Encryption: To achieve this we will need a plaintext (message) and the secret key. We will use a particular encryption algorithm and give the plaintext and key as input. As an output, we will get a ciphertext(encrypted message).
Decryption: To recover the original message (plaintext) from the ciphertext (encrypted message), we will use a decryption algorithm which will be the reverse process of the encryption algorithm. We will give ciphertext and the same secret key as input. As an output, we will get an original message.
To understand this better, let’s take an example…
Suppose,
Plaintext (message) = m
Secret key = k
Ciphertext (encrypted message) = c
Encryption algorithm is chosen = XOR
So according to encryption definitely,
c = m ⊕ k
I hope you have the idea about xor operation. Don’t get confused about how to do xor of alphabets, just find the ASCII value of each character and convert it into the binary. Sounds lengthy but I hope you are thinking to write code instead of using pen and paper.
Well, for getting back our plaintext from the ciphertext…
m = c ⊕ k
You can verify this equation by putting c = m ⊕ k and k ⊕ k will be zero.
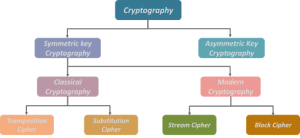
There are lots of types of cryptography (encryption algorithm). Discussing all here won’t be possible. I will just put the picture here to give you a basic idea about the structure of cryptography.
Secret key? Why it is secret?
There are two types of key encryption.
Symmetric key encryption: in this case, the key used for encryption will be the same as the key used for decryption.
Asymmetric key encryption: in this case, the encryption key and decryption key will be different.
Note: the example we took above is symmetric key encryption.
Why do we call this key a secret key?
Obviously, it has to be secret. What if it is not secret?
Suppose there are two persons Alice and Bob wants to communicate secretly. Alice encrypted a message and send that ciphertext to Bob. There is an eavesdropper Mallory who will be able to see ciphertext. Now, if the key is not secret, Mallory can perform the decryption process and get the plaintext. So the communication will no longer be a secret.
CONCLUSION :
This blog contained history and fundamental information about cryptography. Covering everything in a single blog is not possible but I believe it was a good kick start.
Talking about the nonsense I wrote at the start of the blog, I have encrypted it using Caesar Cipher. If you wanna know what is the meaning of that you can decrypt it using this online tool: https://www.dcode.fr/caesar-cipher
Also, you can go through my codes for the implementation of different Cryptography methods. Link: https://github.com/Amangondaliya555/Crypto.git
Keep Reading, keep learning!
TEAM CEV